Certifications
AWS Certified Developer - Associate
AWS Certified Solutions Architect - Associate
IAM
- Users and user groups — human identities
- Roles — credentials provided by a Role are temporary and automatically rotated by AWS. Use roles over long-lived access keys wherever possible
- Policies — JSON documents that define permissions. Attach to users, groups, or roles
- Principle of least privilege — start with no permissions and grant only what’s needed
Compute
EC2
- Virtual machines with full OS control
- Instance types optimised for different workloads (compute, memory, storage, GPU)
- Spot instances — up to 90% cheaper, but can be interrupted. Good for batch processing, CI/CD
- Reserved instances / Savings Plans — commit for 1-3 years for significant discounts
Lambda
- Serverless functions, pay per invocation
- Max 15 minute execution time — limits
- Cold starts can be a problem for latency-sensitive workloads
- Good for event-driven architectures, glue code, and lightweight APIs
ECS / EKS
- ECS — AWS-native container orchestration. Simpler than Kubernetes, tightly integrated with AWS
- EKS — managed Kubernetes. Use when you need K8s compatibility or are already invested in the K8s ecosystem
- Fargate — serverless compute for containers (no EC2 instances to manage)
Storage
S3
- Object storage, practically unlimited capacity
- Storage classes: Standard, Infrequent Access, Glacier (archival)
- Versioning, lifecycle policies, cross-region replication
- Use presigned URLs for temporary access to private objects
EBS
- Block storage volumes for EC2
- Persist independently from EC2 instance lifecycle
- Snapshot for backups
Networking
VPC
- For a region e.g.
eu-west-1 - One or more subnets in each availability zone
- Each subnet has a route table associated with it that tells network traffic where to go
- Network ACL (access control list) on the VPC — stateless firewall for subnets. If you allow inbound traffic on port 80, you must also create a corresponding outbound rule to allow the response traffic on the appropriate port range (ephemeral ports). The ACL inspects each packet in isolation, without considering previous packets
- Internet gateway (IGW) to make a subnet public
- NAT gateway — allows private subnets to reach the internet without being publicly accessible
Security Groups
- Stateful — when you allow inbound traffic on a certain port (e.g., port 80 for HTTP), the Security Group automatically allows the return traffic from the instance on an ephemeral port. It “remembers” the initial request
A complete Security Group rule has three pieces:
- Type: The kind of traffic (e.g., TCP, which is used for most database connections)
- Port: The specific “door” for that traffic. For a MySQL database, this would be port
3306 - Source: This is the clever part. Instead of using the web server’s specific IP address, we can use the web server’s own Security Group as the source
So, the rule on the database’s Security Group would look like this:
- Allow traffic of type TCP on port 3306 but only from sources that are part of the web-server-security-group
Route 53
- DNS service — can route to AWS resources or external endpoints
- Health checks and DNS failover
- Routing policies: simple, weighted, latency-based, geolocation, failover
Messaging
SQS
- Pull-based (consumers poll for messages)
- 1 to 1
- Standard (at-least-once delivery, best-effort ordering) vs FIFO (exactly-once processing, strict ordering)
- Dead-letter queues for failed messages
- See Queues for general concepts
SNS
- Fan-out (messages are pushed to subscribers)
- 1 to many
- Subscribers can be SQS queues, Lambda, HTTP endpoints, email
EventBridge
- Serverless event bus
- Rule-based routing to targets
- Good for decoupled, event-driven architectures
Data
RDS
- Managed relational databases (PostgreSQL, MySQL, MariaDB, Oracle, SQL Server)
- Multi-AZ for high availability
- Read replicas for read scaling
DynamoDB
- Managed NoSQL (key-value and document)
- Single-digit millisecond latency at any scale
- Pay per request or provisioned capacity
- Global tables for multi-region
Glue
- Serverless ETL service
- Supported data file sources
Other Services
Step Functions
- Orchestrate workflows as state machines — docs
- Good for coordinating Lambda functions and long-running processes
CloudFront
- CDN — caches content at edge locations globally
- Works with S3, EC2, ALB, or any HTTP origin
CloudWatch
- Monitoring, logging, and alerting
- Custom metrics and dashboards
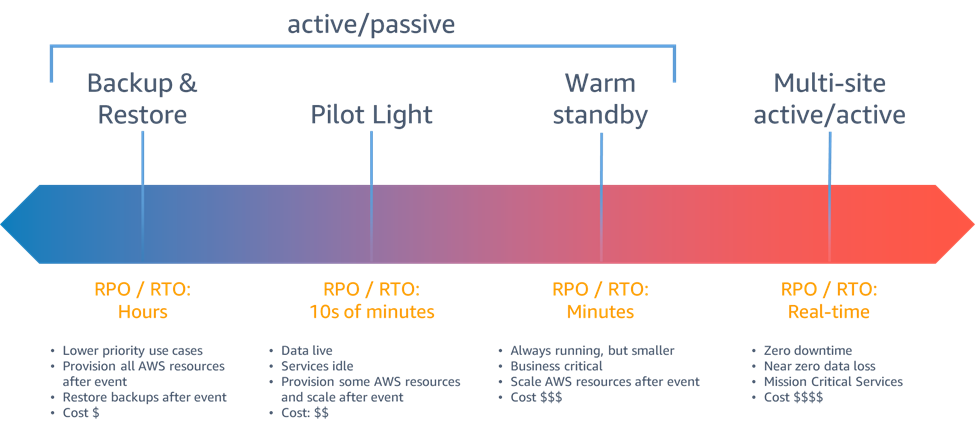
Disaster Recovery
- DR options in the cloud
- See also: Disaster Recovery